Norton Power Eraser 5.3.0.47 is an easy-to-use software that helps users quickly remove threats from..
5.3.0.47| License: Free |
| Released: Symantec |
| Request: Windows XP/Vista/7/8/8.1/10 |
| Last updated: 07-09-2021 |
| OS: Window |
| Version: 5.3.0.47 |
| Total download: 5605 |
| Capacity: 9,2 MB |
Norton Power Eraser 5.3.0.47 is an easy-to-use software that helps users quickly remove threats from their own Windows computers. In addition, it also adds an extra layer of security to their system. Besides, new users will not face any difficulty while manipulating and using the program because Norton Power Eraser has a relatively intuitive interface.
The main window of the program provides the user with a clear and intuitive view. In addition, it supports instant access to 3 main components of Power Eraser: scanning for potentially dangerous files, undoing previous repairs, and reconfiguring advanced settings.
By default, you will be able to use this tool to browse your computer and find various threats and rootkits. It will show the description, category and status for each category, and the action that needs to be initiated, such as deleting it. Remember that a computer restart may be required to complete the task, so save any previous projects.
Also, you will be able to ask the program to create a system restore point before attempting to resolve the issue. Just in case Windows starts experiencing stability issues, you need to undo the settings. Meanwhile, the information related to the log file can be viewed in a separate file and its location will be displayed in Windows Explorer without the user needing to leave the interface.
Switching to advanced scan mode provides additional functionality. For example, you'll be able to run a scan with Norton Cloud to verify a detailed file or folder and find out what the Norton community thinks about it. Then, perform a standard scan by looking at files in Windows, as well as initiate a search on the PC if there are multiple versions of Windows installed on it.
This application helps you to apply proxy server configuration, change default log file storage folder, enable multi-boot check mode, show only bad files and exclude rootkit scanning mode (required) system restart request). In addition, you will be able to clear the log file history to free up more storage space and restore all settings to their original parameters.
As such, Norton Power Eraser is a useful program, although it seems more suitable for experienced users. Even so, beginners can still install it without risk thanks to its intuitive design interface and help file.
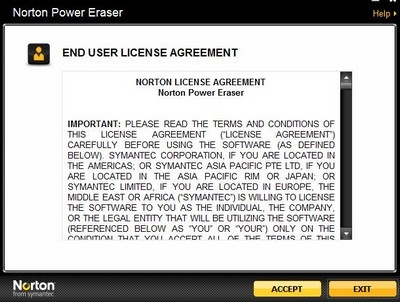
After downloading, activate the software, press Accept in the terms dialog to get started right away without installation.
Click the Scan button in the main interface of the software to start scanning and checking for viruses. The software provides 2 scanning modes:
- System Scan: scan all systems.
- Directory Scan: scans optional drives and folders.
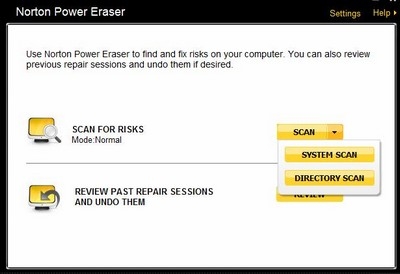
Depending on the purpose you have to check, select the appropriate scan mode. The process of scanning for software viruses is quite fast, faster than most current anti-virus software.
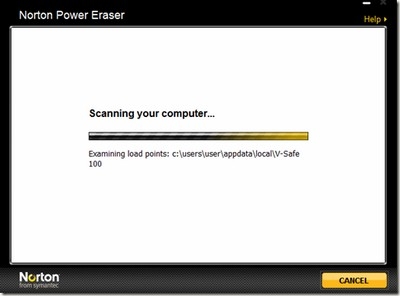
After the scan is finished, a list of viruses/malware (if any) will be listed. Tick the option 'Create System Restore Point' (to create a restore point in case the antivirus affects the system) then press the Fix button Let Norton Power Eraser start the removal process.
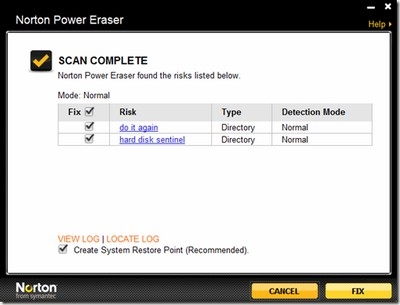
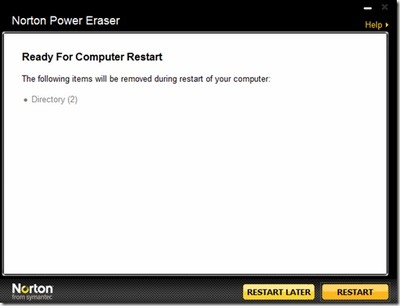
The software will create a restore point and begin to overcome the consequences of the virus. After this process is finished, the software will ask you to restart the computer to complete the search and kill process.
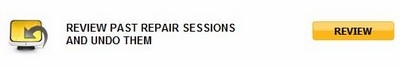
In the event that after virus removal, the system is unstable (because the anti-virus process can affect previously infected system files), you press the Review< /strong> on the main interface of the software, find the previous activity milestones to restore the state of the system as before the activities took place.
In general, Norton Power Eraser is a useful tool to keep in your "weapons", and a useful assistant to other anti-virus software in the battle against attack and vandalism. of computer viruses.
5
4
3
2
1